Our critical infrastructure is at an inflection point. Hackers and nation-state actors have targeted the systems that underpin our everyday lives. Predominant cybersecurity practices can’t adequately protect operations from these threats. We need a new way forward.
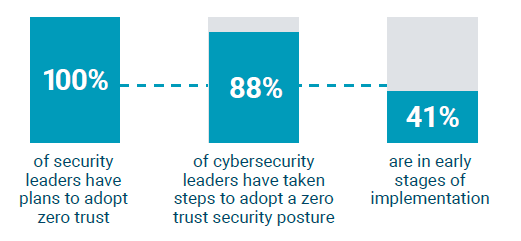
The industrial world is taking action. Cybersecurity leaders recognize the potential of zero trust, and an overwhelming majority are in the process of adopting a zero-trust strategy. This is a major shift from reactive to proactive cybersecurity.
Until recently, new security solutions serving real-world operations had been primarily focused on visibility and threat detection. But those tools can’t prevent hacks from happening—they only monitor for and raise the alert once an attack is underway. Alternatively, implementing a zero-trust architecture creates an environment where hacking attempts are blocked outright, or contained and mitigated.
Those who have started implementing zero trust strategies are reaping benefits that extend beyond protection from cyberattacks. By adopting a zero-trust architecture, operators are expediting digital transformation efforts. When an operator assigns every asset or data stream an identity that can be managed centrally, they’re also enabling remote access, efficient data sharing, and convenient collaboration with partners. Zero trust adoption is inevitable across the industry – it is happening, and it is happening now.
Implementing zero trust is a years-long process, but one that Three Wire can help you with! Contact our experts today to learn more.
*Data from July 2022 • Wakefield Research


